On this page
- Before you begin
- Overview
- Passwords at a glance
- Important notes
- Step 1: Combine the certificate files
- Step 2: Package with OpenSSL (PKCS12)
- Step 3: Convert to Java Key Store (JKS)
- Step 4: Configure MCS
- Troubleshooting
Before you begin
Have the following ready before starting. Missing any of these mid-process is the most common cause of having to restart the tutorial.
- From your certificate authority (CA): either
- a pair of certificate files (
yourdomain.com.crtandIntermediateCA.crt), or - a single
.pemfile (yourdomain.com.pem).
- a pair of certificate files (
- The matching private key (
yourdomain.com.key) from the same CA request. This is required in either case. - A Windows machine with administrator rights (to edit the PATH environment variable). These steps are done on Windows even if MCS itself runs on Linux. The resulting JKS file is portable.
- Access to the MCS server's filesystem to copy the final JKS file into
/MCS root/data/and edithttps.ini. - MCS version 10.1a or above. HTTPS support was introduced in this release.
Allow roughly 15–20 minutes end-to-end, plus any time needed to install OpenSSL and a JDK if they are not already on the machine.
Overview
You will chain four files together: the CA-issued certificates and your private key are bundled into a PKCS12 archive, converted into a Java Key Store, and then referenced by an MCS config file.
or .pem
(OpenSSL)
(keytool)
https.ini
(MCS config)
Support: if you hit an issue, check the troubleshooting section or send an email.
Passwords at a glance
The same password is used at four prompts across Steps 2–4. Choosing it once and re-using it everywhere is the simplest path; mismatches are the most common cause of HTTPS failing to come up at runtime.
| Where you are prompted | What to enter |
|---|---|
| Step 2 (OpenSSL "Enter Export Password:") | Choose a new password now. |
Step 3 (keytool "Enter destination keystore password:") |
The same password as Step 2. |
Step 3 (keytool "Enter source keystore password:") |
The same password as Step 2. |
Step 4 (SSLPassword= in https.ini) |
The same password as Step 2. |
MCS-specific constraint: the password must be 8–16 characters and contain only letters and numbers. Special characters are not currently supported by the MCS https.ini parser.
Important notes
About the JKS format: Java considers the JKS keystore format deprecated in favour of PKCS12 (since Java 9), and keytool will emit a warning to that effect when the JKS file is created in Step 3. This warning is expected and can be ignored. MCS currently requires a JKS file. Direct PKCS12 support is planned for a future MCS release, which will remove the need for Step 3.
Platform: these steps are documented on Windows. The resulting JKS file is portable and works with MCS on both Linux and Windows. Performing the build on Windows is recommended even if MCS is installed on Linux.
Step 1 of 4Combine the Certificate Files
Concatenate the two CA-issued certificate files into one, so OpenSSL can read them as a single input in the next step.
A valid SSL certificate provided by the issuing certificate authority is required. It will normally consist of two files, for example yourdomain.com.crt and IntermediateCA.crt.
Already have a .PEM file? Some CAs provide a single .pem (for example yourdomain.com.pem) instead of two .crt files. In that case, skip directly to Step 2 and use the PEM method there.
Either way, the matching yourdomain.com.key private key file is still required in Step 2.
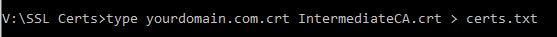
Combine the two .crt files:
- Create a folder on the Windows desktop (or other suitable location).
- Place both certificate files inside that folder.
- Open a Windows command prompt and
cdinto the folder. - Run:
Certificate order matters: the end-entity certificate (your domain) must come first, followed by the intermediate CA.type yourdomain.com.crt IntermediateCA.crt > certs.txt - Verify that
certs.txtwas created in the same folder.
Leave the command window open for use in Step 2.
Step 2 of 4Package with OpenSSL into a PKCS12 File
Bundle the combined certificate with your private key into a single password-protected PKCS12 archive that keytool can import in Step 3.
This step requires OpenSSL for Windows (scroll to the "Download Win32 OpenSSL" section on that page). OpenSSL 3.x is current; the command syntax below works on both 1.1.1 and 3.x.
- Download and install the full OpenSSL installer for your architecture (32-bit or 64-bit). Skip if already installed.
- Locate the
bindirectory in the install folder. On 64-bit systems this is typicallydrive:\OpenSSL-Win64\bin. - Add that
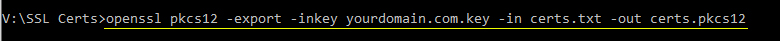
bindirectory to the Windows PATH environment variable soopensslresolves from your command prompt. - Run the command that matches your input files:
CRT method (using the combined
certs.txtfrom Step 1):openssl pkcs12 -export -inkey yourdomain.com.key -in certs.txt -out certs.pkcs12PEM method (if your CA provided a
.pem):openssl pkcs12 -export -inkey yourdomain.com.key -in yourdomain.com.pem -out certs.pkcs12 - When prompted for "Enter Export Password:", choose an alphanumeric password of 8–16 characters and re-enter it to confirm. Remember this password. You will use it at three more prompts (see Passwords at a glance).
- Verify that
certs.pkcs12was created in the same folder.
Leave the command window open for use in Step 3.
Step 3 of 4Convert the PKCS12 into a Java Key Store (JKS)
Use Java's keytool to convert the PKCS12 archive into the Java Key Store format that MCS reads at startup.
This step requires the Java keytool utility, which ships with any standard JDK distribution.
- If a JDK is not already installed, download and install a current LTS release. Any standard distribution is supported, for example Eclipse Temurin, Amazon Corretto, Azul Zulu, Microsoft Build of OpenJDK, or Oracle JDK.
- Add the JDK
bindirectory to the Windows PATH environment variable. - Run:
keytool -importkeystore -srckeystore certs.pkcs12 -srcstoretype PKCS12 -destkeystore certs.jks -deststoretype JKS - You will be prompted three times. Enter the same password you chose in Step 2 at each prompt (see Passwords at a glance):
- For "Enter destination keystore password:", enter your Step 2 password.
- For "Re-enter new password:", enter the same again.
- For "Enter source keystore password:", enter the same again (this is the existing PKCS12 password).
V:\SSL Certs>keytool -importkeystore -srckeystore certs.pkcs12 -srcstoretype PKCS12 -destkeystore certs.jks -deststoretype JKS
Enter destination keystore password:
Re-enter new password:
Enter source keystore password:
Entry for alias 1 successfully imported.
Import command completed: 1 entries successfully imported, 0 entries failed or cancelledkeytoolwill typically print: "Warning: The JKS keystore uses a proprietary format. It is recommended to migrate to PKCS12...". This is expected and safe to ignore. MCS currently requires JKS. See Important notes.- Verify that
certs.jkshas been created in the same folder, ready for use in Step 4.
Step 4 of 4Configure MCS to Use the JKS File
Point MCS at the new JKS file via https.ini, tighten file permissions on Linux, and restart.
- On the MCS server, navigate to the
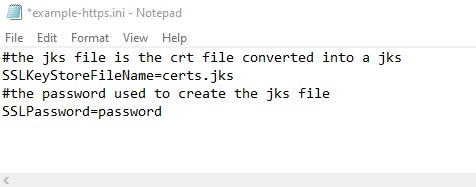
/MCS root/data/directory. The same JKS file works on both Linux and Windows installations. - First-time setup only: rename
example-https.initohttps.ini. - Copy the
certs.jksfile from Step 3 into/MCS root/data/. - Edit
https.iniand set:SSLKeyStoreFileNameto thecerts.jksfilename.SSLPasswordto the password you chose in Step 2 (see Passwords at a glance).
Linux file permissions: certs.jks and https.ini contain sensitive material. The JKS keystore password is stored in plaintext inside https.ini. On Linux, restrict access to the user that MCS runs as:
chown mcs:mcs certs.jks https.ini
chmod 600 certs.jks https.iniReplace mcs:mcs with the actual user and group that the MCS service runs under on your system. chown must be applied before chmod 600, otherwise MCS will not be able to read the files once the permissions are tightened.
Stop and restart MCS to load the new certificate. Once enabled, only HTTPS traffic will be authorized and any login request initiated over HTTP will be automatically redirected to HTTPS. Port 80 remains open for those redirects and for high-performance MCS hardware/software satellites that rely on it for test accuracy.
You're done. After restart you should have:
certs.jksandhttps.iniin/MCS root/data/(with tightened permissions on Linux).SSLKeyStoreFileNameandSSLPasswordset inhttps.ini.- MCS stopped and restarted.
Browse to https://<your-mcs-hostname>/ to confirm. If HTTPS does not come up, see Troubleshooting below.
Troubleshooting
- Passwords used throughout the process must match exactly and contain only letters and numbers (MCS-specific constraint: special characters are not currently supported by the
https.iniparser). - Verify that the password specified in the
https.inifile matches the one used for the certificate JKS file. The destination (JKS) password set in Step 3 and the source (PKCS12) password set in Step 2 must also match each other. - Ensure that the JKS filename specified in
https.iniis correct and that the file exists in the/MCS Root/data/directory. - On Linux, confirm that
certs.jksandhttps.iniare readable by the user the MCS service runs as. If you tightened permissions withchmod 600, the files must be owned by that user. - Confirm that the installed JDK is a current stable LTS release. Issues have been reported with early access (EA) and release candidate (RC) versions. Any standard OpenJDK distribution (Temurin, Corretto, Zulu, Microsoft, Oracle) is supported.
Detecting the JDK type installed
Check the Java version:
java --versionIf the output does not explicitly state EA or RC, check the package manager:
Debian / Ubuntu:
apt list --installed | grep openjdkRed Hat / Fedora:
dnf list installed | grep javaArch Linux:
pacman -Q | grep jdkSome Java distributions (including OpenJDK) store version details under /usr/lib/jvm/:
ls -l /usr/lib/jvm/- Check the MCS console log located in
/MCS Root/logs/. If MCS encounters an issue verifying the certificate, details will be recorded there.

