Server Security Protocols
Physical Server Disk Protection
Any unauthorized access to the Satellite interface is safeguarded against. The architecture ensures that unauthorized entities cannot access the physical server disk or file system. The Satellite operates strictly within its designated working directory, with no interactions beyond this domain.
MCS and Data Security Protocols
MCS Host Protection
Should an unauthorized party access the Satellite interface, they would be unable to reach the MCS host. While the URL or IP of the host may be visible, this information alone is insufficient for access — secured password authentication is mandatory.
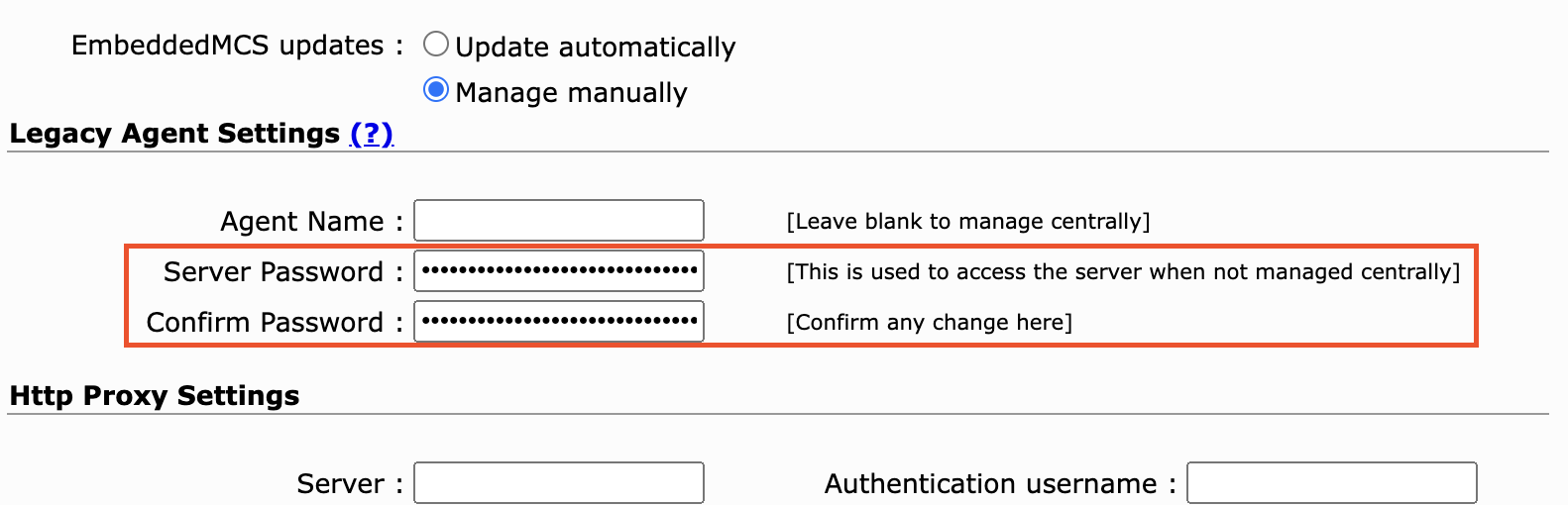
Legacy Agent Settings
For legacy purposes, agent settings display an encrypted, obfuscated password pertinent only to older MCS engines. This encrypted password does not grant access to MCS — it functions solely as an authorization mechanism for MCS to process work orders.
Data Privacy
No private data traverses through a Satellite. The sole data exchanged between MCS and the Satellite pertains exclusively to the tests in operation.

